by Simantini Singh Deo
8 minutes
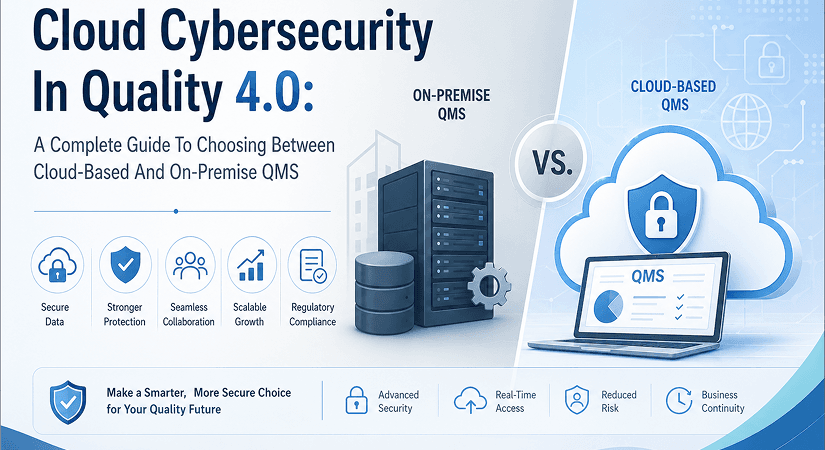
Cloud Cybersecurity In Quality 4.0: A Complete Guide To Choosing Between Cloud-Based And On-Premise QMS
A complete guide to cloud vs on-premise QMS in pharma cybersecurity, GAMP categories, Quality 4.0 readiness and the deciding factors explained.
As industries transition toward the era of Quality 4.0, organizations are increasingly embracing digital technologies, interconnected systems, and automated workflows to remain competitive and compliant. The modern approach to quality management is no longer limited to documentation and periodic audits; instead, it focuses on real-time visibility, predictive analytics, and seamless collaboration across departments and geographies.
Among these advancements, the shift from traditional on-premise Quality Management Systems (QMS) to cloud-based QMS platforms stands out as one of the most transformative developments in recent years. With this shift, however, comes an important and often debated question: how do cybersecurity considerations influence this decision?
Many organizations are naturally drawn to the scalability, flexibility, and accessibility that cloud systems offer. Teams can collaborate in real time, data can be accessed instantly, and system upgrades happen without operational disruptions. Despite these benefits, hesitation persists due to concerns surrounding data breaches, unauthorized access, regulatory scrutiny, and overall control of sensitive information.
On the other hand, on-premise systems provide a sense of ownership and control but introduce challenges related to cost, maintenance, and long-term sustainability. To make an informed and strategic decision, organizations must not only understand how these two systems differ functionally but also evaluate how cybersecurity responsibilities and risks are distributed in each model.
This comprehensive guide explores these differences in detail, explains the cybersecurity implications, and highlights why cloud-based QMS platforms are increasingly becoming the preferred choice for organizations embracing Quality 4.0.
Cloud-Based QMS Vs. On-Premise QMS: Understanding The Differences
Before diving deeper into cybersecurity, it is essential to clearly understand how cloud-based and on-premise QMS systems operate. While both systems serve the same fundamental purpose, managing quality processes such as document control, audits, training, deviations, and CAPA, their underlying architecture and operational responsibilities differ significantly.
What Is A Cloud-Based QMS?
A cloud-based QMS operates on a Software as a Service (SaaS) model, where the vendor hosts the system on remote servers and delivers it to users via the internet. The vendor is responsible for managing system performance, updates, security, and overall infrastructure, allowing organizations to focus purely on quality processes rather than IT management.
1) Access To A Cloud-Based QMS
A cloud-based QMS can be accessed from any location using an internet-enabled device such as a laptop, tablet, or smartphone. This level of accessibility enables employees, auditors, and stakeholders to collaborate in real time regardless of their physical location. It is particularly beneficial for organizations with multiple sites or remote teams, as it ensures consistent data availability and streamlined communication across the organization.
2) Infrastructure Needs For A Cloud-Based QMS
Organizations do not need to invest in physical infrastructure such as servers, storage devices, or data centers. The vendor takes care of hosting, system maintenance, backups, and upgrades. This not only reduces the burden on internal IT teams but also ensures that the system is always running on the latest and most secure version without manual intervention.
3) Payment Terms For A Cloud-Based QMS
Cloud-based QMS solutions follow a subscription-based pricing model, typically billed monthly or annually. These costs usually include system access, hosting, security, maintenance, and upgrades. Pricing often depends on the number of users, making it scalable and adaptable to organizational growth or changes in workforce size.
4) Cybersecurity Responsibilities In A Cloud-Based QMS
In this model, while the organization retains ownership of its data, the responsibility for securing that data lies with the vendor. This includes implementing encryption, managing secure access controls, ensuring regulatory compliance, maintaining audit trails, and protecting against cyber threats. Organizations benefit from the vendor’s specialized expertise and dedicated security resources.
5) Accounting For Cloud QMS Expenses
Expenses related to a cloud-based QMS are categorized as operational expenses (OPEX). This allows organizations to avoid large upfront investments and instead manage costs as part of their ongoing operational budget.
What Is An On-Premise QMS?
An on-premise QMS is installed and operated within the organization’s own IT infrastructure. The organization purchases the software through a one-time license and is responsible for hosting, maintaining, and securing the system.
1) Access to An On-Premise QMS
Access to an on-premise QMS is typically limited to the organization’s internal network. Employees must be physically present within the network environment unless remote access solutions are configured, which can introduce additional complexity and security concerns.
2) Infrastructure Needs For An On-Premise QMS
Organizations must invest heavily in hardware, including servers, storage systems, networking equipment, and backup solutions. Additional requirements include power supply systems, cooling infrastructure, and physical data center space. These components must be maintained, updated, and periodically replaced, adding to long-term costs.
3) Payment Terms For An On-Premise QMS
While the software is purchased through a one-time license fee, organizations often incur ongoing costs for maintenance, technical support, and upgrades. These recurring expenses can significantly increase the total cost of ownership over time.
4) Cybersecurity Responsibilities In An On-Premise QMS
The responsibility for cybersecurity rests entirely with the organization. Internal IT teams must implement security measures, monitor systems, apply updates, and respond to threats. This requires skilled personnel, robust processes, and continuous investment in cybersecurity infrastructure.
5) Accounting For On-Premise QMS Expenses
On-premise QMS costs are classified as capital expenditures (CAPEX), as they involve significant upfront investment in infrastructure and software.
Cybersecurity Challenges In An On-Premise QMS
Despite the perception that local data storage offers better control, on-premise systems present several cybersecurity challenges that organizations must address.
- Full Cybersecurity Responsibility: Organizations must establish and enforce strict controls over data access, modification, and deletion. They must maintain secure audit trails, ensure data integrity, and demonstrate compliance during regulatory inspections. Since all responsibility lies internally, any weaknesses in security practices can lead to significant compliance risks and audit findings.
- Increased Validation Requirements: On-premise systems often require extensive customization to align with business processes. Such systems fall under GAMP Category 5, which is associated with the highest level of risk. As a result, organizations must conduct comprehensive Computer System Validation (CSV), including detailed testing, documentation, and ongoing verification. This increases both complexity and resource requirements.
Cybersecurity Benefits Of A Cloud-Based QMS
Cloud-based QMS platforms have evolved significantly and now offer advanced security capabilities that often surpass those of traditional on-premise systems.
a) Secure Remote Data Hosting
Cloud providers use highly secure data centers with advanced encryption, continuous monitoring, and automated backup systems. These facilities are designed to ensure data availability, integrity, and protection even in the event of system failures or cyberattacks.
b) Access To Specialized Cybersecurity Experts
Cloud vendors employ dedicated teams of cybersecurity professionals who monitor systems around the clock, respond to threats in real time, and continuously improve security measures. This level of expertise is difficult for most organizations to maintain internally.
c) Reduced Internal Data Tampering Risks
Because data is stored remotely and managed by the vendor, employees cannot directly access or manipulate backend systems. This significantly reduces the risk of internal data tampering and ensures stronger data integrity.
d) Simplified Compliance Requirements
Cloud-based QMS solutions typically fall under GAMP Category 3 or 4, which require fewer validation steps compared to Category 5 systems. This simplifies compliance efforts and reduces the overall burden on organizations.
Modern Approaches To Cloud Cybersecurity
Cloud-based quality management systems rely on a multi-layered cybersecurity framework designed to safeguard sensitive data, maintain system integrity, and protect against unauthorized access. This approach typically combines infrastructure-level defenses, application-layer controls, and continuous monitoring to create a robust security posture suitable for regulated environments.
As threats grow more sophisticated, cloud providers continue to enhance their capabilities, ensuring that organizations can depend on modern, resilient, and intelligently designed protection mechanisms. This makes cloud cybersecurity not just a defensive tool but a key enabler of operational continuity and regulatory compliance.
A) Web Application Firewall (WAF): A Web Application Firewall is commonly integrated with the platform’s Application Load Balancer to analyze and filter incoming traffic. It helps identify and block malicious requests, detect unusual access patterns, and prevent attempts to exploit application vulnerabilities.
By examining traffic in real time, a WAF can respond immediately to injection attempts, cross-site scripting attacks, and other common threats. In many systems, CAPTCHA verification is automatically triggered for repeated login attempts, adding an extra layer of protection against automated attacks or unauthorized access attempts.
This automated behavior ensures that even during peak activity or attempted breaches, system defenses remain active, dynamic, and capable of differentiating legitimate users from malicious actors.
B) Application-Level Security Controls: Cloud systems usually enforce well-defined login security protocols to mitigate the risk of unauthorized access. For example, user accounts may be temporarily blocked after a specific number of failed login attempts, often five, and permanently blocked after a higher threshold, such as ten attempts.
These strict application-level controls significantly reduce the likelihood of brute-force attacks and ensure that only legitimate users can access the system. In addition to login management, many platforms integrate strong password policies, session timeout rules, and multi-factor authentication to further secure entry points.
Together, these measures create a controlled, traceable, and layered security environment that minimizes user-related vulnerabilities and strengthens overall system protection.
C) Continuous Monitoring And Security Updates: Modern cloud environments are monitored continuously using automated tools and real-time analytics that detect threats, vulnerabilities, or suspicious activity. This constant surveillance allows potential issues to be identified early, often before they can cause operational impact.
Security protocols are routinely updated to align with evolving cyber risks, regulatory expectations, and industry best practices. By continuously adjusting defenses, whether patching software, updating firewalls, or enhancing intrusion detection capabilities, cloud platforms ensure they can respond quickly to emerging threats.
This proactive and dynamic approach ensures the platform remains secure, resilient, and capable of addressing newly emerging risks while maintaining uninterrupted service availability.
Cybersecurity As The Deciding Factor
While factors such as cost efficiency, scalability, infrastructure requirements, and operational convenience all influence the choice between cloud-based and on-premise QMS solutions, cybersecurity often becomes the ultimate differentiator.
Cloud environments generally benefit from advanced security architecture, specialized security teams, and continuous threat monitoring, capabilities that most organizations struggle to replicate internally. With cyberattacks growing in frequency and sophistication, having access to enterprise-level protections is no longer optional but essential.
As a result, cloud-based systems often provide stronger, more reliable, and more future-ready protection for critical quality and compliance data. This positions them as the safer long-term choice for organizations looking to maintain both operational resilience and regulatory readiness in an increasingly digital and threat-prone environment.
In Conclusion
When comparing cloud-based and on-premise QMS platforms, cybersecurity clearly stands out as the defining variable and the ultimate decision-making factor for modern organizations. Cloud-based solutions offer advanced security features, reduced compliance complexity, and lower infrastructure costs, all while ensuring that systems remain continuously updated and protected against evolving cyber threats.
On-premise systems, while providing a sense of control, require substantial investment in infrastructure, skilled personnel, and ongoing maintenance, along with the full burden of managing cybersecurity risks internally. In addition to these considerations, cloud-based QMS platforms align more effectively with the broader goals of Quality 4.0 by enabling real-time data access, seamless collaboration, and scalability.
They also reduce the complexity associated with system validation, thanks to their alignment with lower-risk GAMP categories. This allows organizations to focus more on improving quality processes rather than managing technical overhead. Ultimately, the choice between cloud-based and on-premise QMS should be guided by long-term strategic goals rather than short-term preferences.
As cyber threats continue to evolve and regulatory expectations become more stringent, relying on advanced, professionally managed cloud infrastructure provides a more resilient and future-ready approach. For organizations looking to enhance data security, streamline compliance, and support digital transformation, a cloud-based QMS offers a clear and sustainable advantage in today’s rapidly changing quality environment.
FAQs
1. How Does Cybersecurity Influence The Choice Between Cloud-Based And On-Premise QMS?
Cybersecurity plays a central role in determining whether a cloud-based or on-premise QMS is the safer long-term choice. Cloud systems benefit from enterprise-grade security controls, continuous monitoring, and specialized cybersecurity teams that most organizations cannot replicate internally. On-premise models place the entire security burden on internal IT teams, increasing complexity, cost, and risk. As cyber threats intensify, many organizations find that cloud platforms provide stronger and more future-proof protection.
2. Is A Cloud-Based QMS More Secure Than An On-Premise QMS?
In most modern environments, a cloud-based QMS offers more advanced and continuously updated security safeguards than traditional on-premise systems. Cloud providers use encrypted data centers, multi-layered defenses, and automated threat detection to maintain a resilient security posture. These protections are monitored and improved in real time by dedicated experts, ensuring rapid response to emerging threats. This allows organizations to rely on robust, professionally managed cybersecurity rather than building and maintaining it alone.
3. What Cybersecurity Responsibilities Shift When Moving From On-Premise To Cloud QMS?
When adopting a cloud-based QMS, the vendor assumes responsibility for infrastructure security, system monitoring, vulnerability patching, backups, and disaster recovery. Organizations retain ownership of their data but no longer need to manage servers, perform manual updates, or maintain complex security configurations. This shift significantly reduces internal workload while improving overall security consistency and reliability. It also allows teams to focus more on quality operations rather than technical risk management.